Why XMPro?
CIO's / IT Teams
Security Standards
XMPro’s Comprehensive Security Measures
In addition to our Zero Trust Architecture, we’ve incorporated several other security aspects into our system

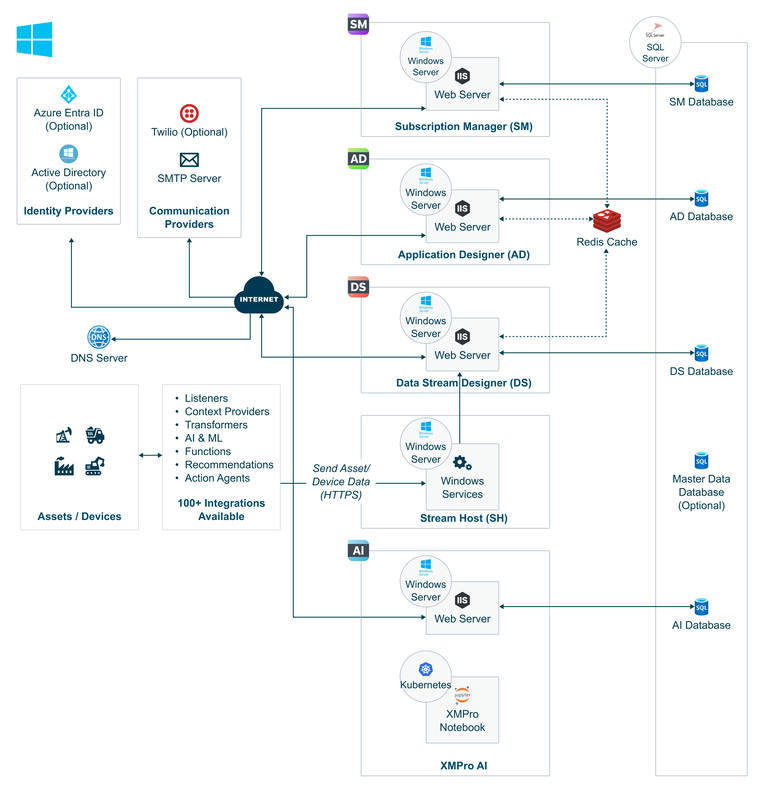
Deployment
Flexible XMPro Deployment.
Bridging Cloud and Edge for Unmatched Flexibility
Deployment Options
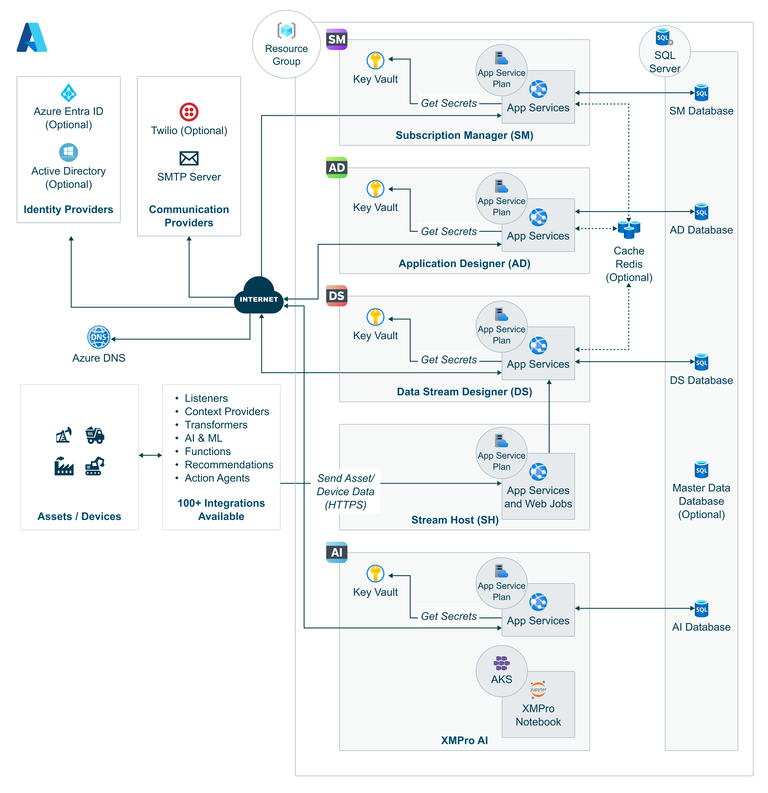
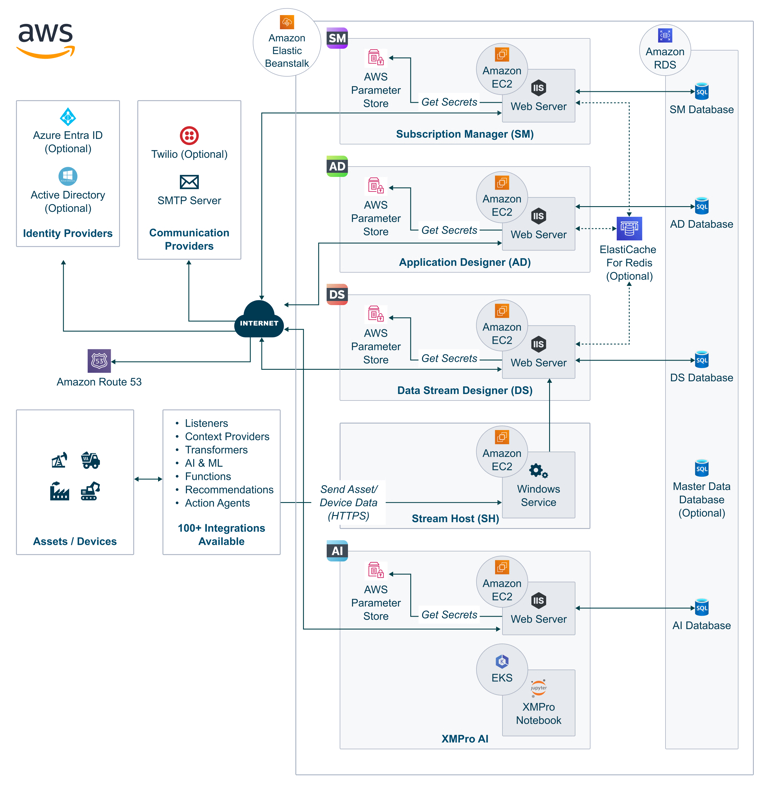
Cloud Deployment
- Azure & AWS: XMPro seamlessly integrates with major cloud platforms like Microsoft Azure and Amazon Web Services (AWS), enabling businesses to leverage the vast computational resources and scalability of the cloud. This option is ideal for organizations looking to minimize on-premise hardware investment while benefiting from the global reach and advanced services of cloud infrastructures.
- Benefits: Cloud deployment offers elasticity, ensuring that resources can be scaled up or down based on demand, enhancing operational efficiency and reducing costs. It also facilitates faster deployment cycles and access to a broad ecosystem of services for analytics, AI, and machine learning.
On-Premise Deployment
- Local Control: For organizations with strict regulatory requirements or those that prioritize data sovereignty, XMPro provides robust on-premise deployment options. This allows businesses to maintain complete control over their infrastructure and data, ensuring compliance with local data protection laws.
- Benefits: On-premise deployment offers the highest level of security and control, making it suitable for industries such as finance, healthcare, and government, where data sensitivity is paramount. It also allows for customization of the physical infrastructure to meet specific performance needs.
Hybrid Deployment
- Best of Both Worlds: Hybrid deployment models combine the flexibility and scalability of cloud services with the control and security of on-premise solutions. XMPro's hybrid deployment option enables businesses to strategically distribute their workloads between cloud and on-premise environments, optimizing performance and compliance.
- Benefits: This approach offers a balanced solution, allowing for scalable analytics and processing in the cloud, while sensitive or critical operations can be kept on-premise. Hybrid deployments provide a pathway for gradual migration to the cloud, enabling organizations to evolve at their own pace.

Edge Vs. Cloud
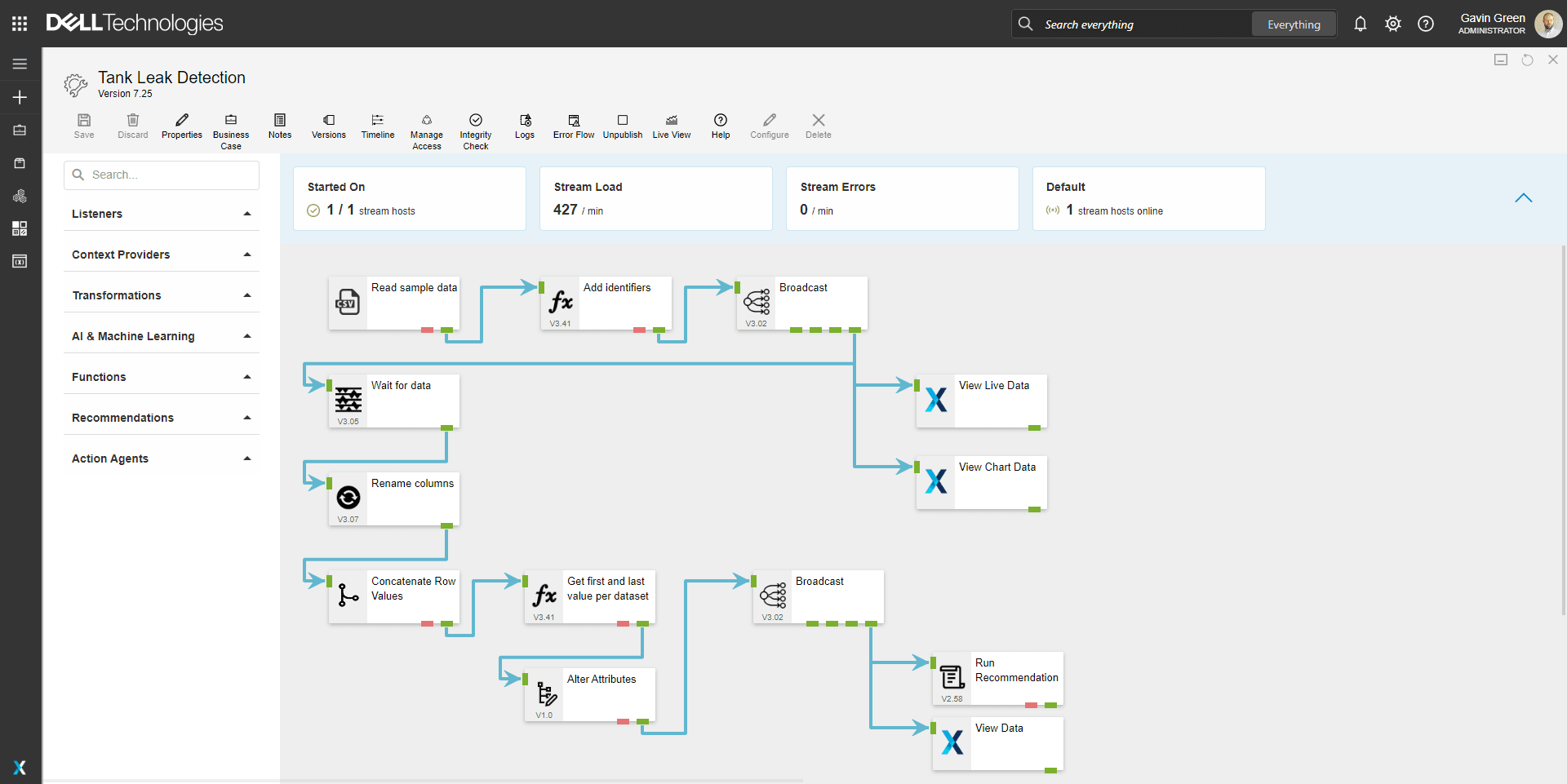
As part of the Dell Validated Design (DVD) for Manufacturing Edge, XMPro runs an advanced edge solution to empower manufacturers to deploy, manage, and scale advanced Digital Twin technologies.
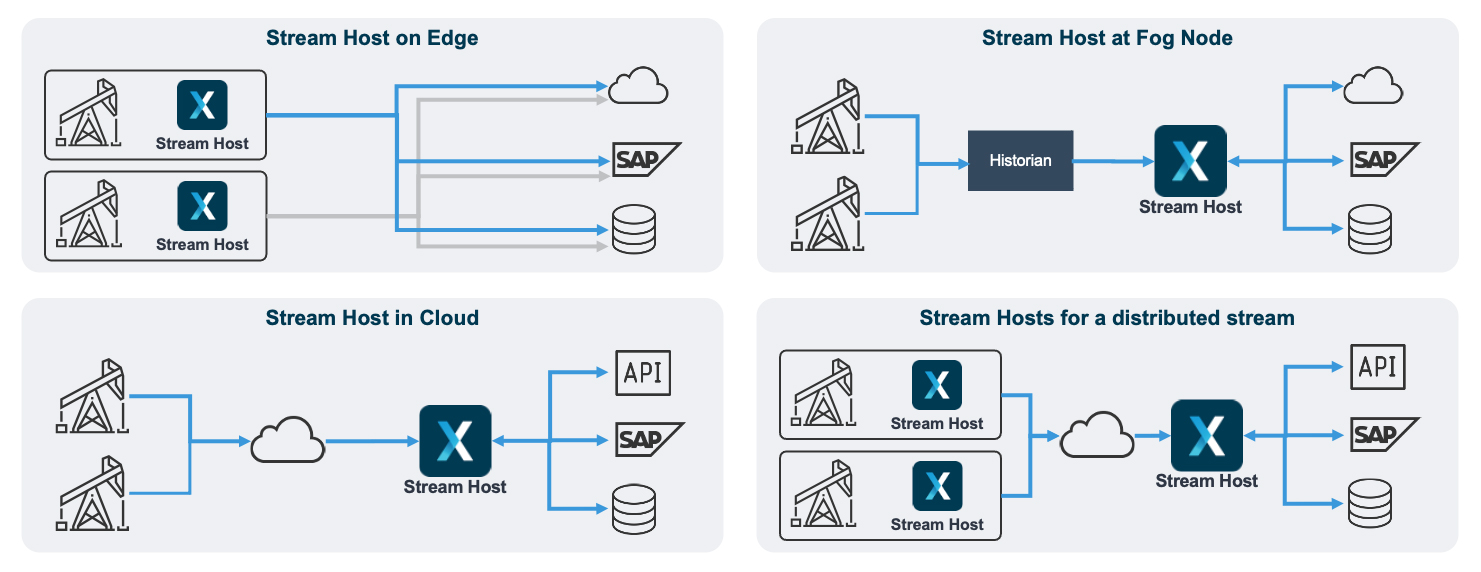
Depending on the Use Case, XMPro can run on different Topologies. Often a blended approach with some components of our platform running on both yields.
Examples:
Dell Validated Design For Manufacturing Edge
XMPro, as a validated Independent Software Vendor (ISV) for Dell's Validated Design for Manufacturing Edge, stands at the forefront of driving innovation and efficiency in smart manufacturing. This collaboration underscores the strategic alignment between XMPro's agile software solutions and Dell's comprehensive, validated manufacturing edge solutions. These solutions are engineered to deliver the speed, scalability, and resiliency essential for achieving superior smart manufacturing outcomes.Integration
User Management

Supporting Zero Trust Architecture
XMPro’s Zero Trust Architecture
In today’s digital age, data security is paramount. At XMPro, we understand the importance of protecting your data. That’s why we’ve implemented a Zero Trust Architecture in our system. This approach assumes no trust and verifies every request as though it originates from an open network. Regardless of where the request comes from or what resource it accesses, Zero Trust teaches us to “never trust, always verify.” What is Zero Trust Architecture? Zero Trust Architecture is a security concept centered on the belief that organizations should not automatically trust anything inside or outside its perimeters and instead must verify anything and everything trying to connect to its systems before granting access. Why Zero Trust Architecture? The Zero Trust model shifts the fundamental paradigm of trust from network-based trust to data- and identity-based trust. This shift provides the following benefits:- Improved Data Security By verifying every access request, regardless of its source, Zero Trust Architecture significantly reduces the risk of data breaches.
- Reduced Insider Threat Risk Zero Trust ensures that every user and device is treated as potentially hostile, regardless of whether they are inside or outside the network.
- Greater Visibility and Control Zero Trust provides detailed logs and analytics, giving you greater insight into your network and data usage patterns.